Operational Technology (OT) networks are under increasing pressure to share data with enterprise systems, cloud analytics platforms, and security monitoring tools. At the same time, industrial operators must ensure that these connections do not introduce cyber risk into critical control systems.
This is exactly the challenge addressed by IEC 63452.
For OT professionals working in energy, utilities, manufacturing, and other critical infrastructure sectors, IEC 63452 provides guidance on how to safely transfer operational data while maintaining strict network isolation.
In this article we’ll explain what the standard covers, why it matters for OT security, and how organisations can approach implementation.
The OT Connectivity Challenge
Modern industrial environments rely on data more than ever before. Operations teams need to move information from control networks to external systems for purposes such as:
- Operational monitoring
- Asset performance analytics
- Remote diagnostics
- Regulatory reporting
- Security monitoring and SIEM integration
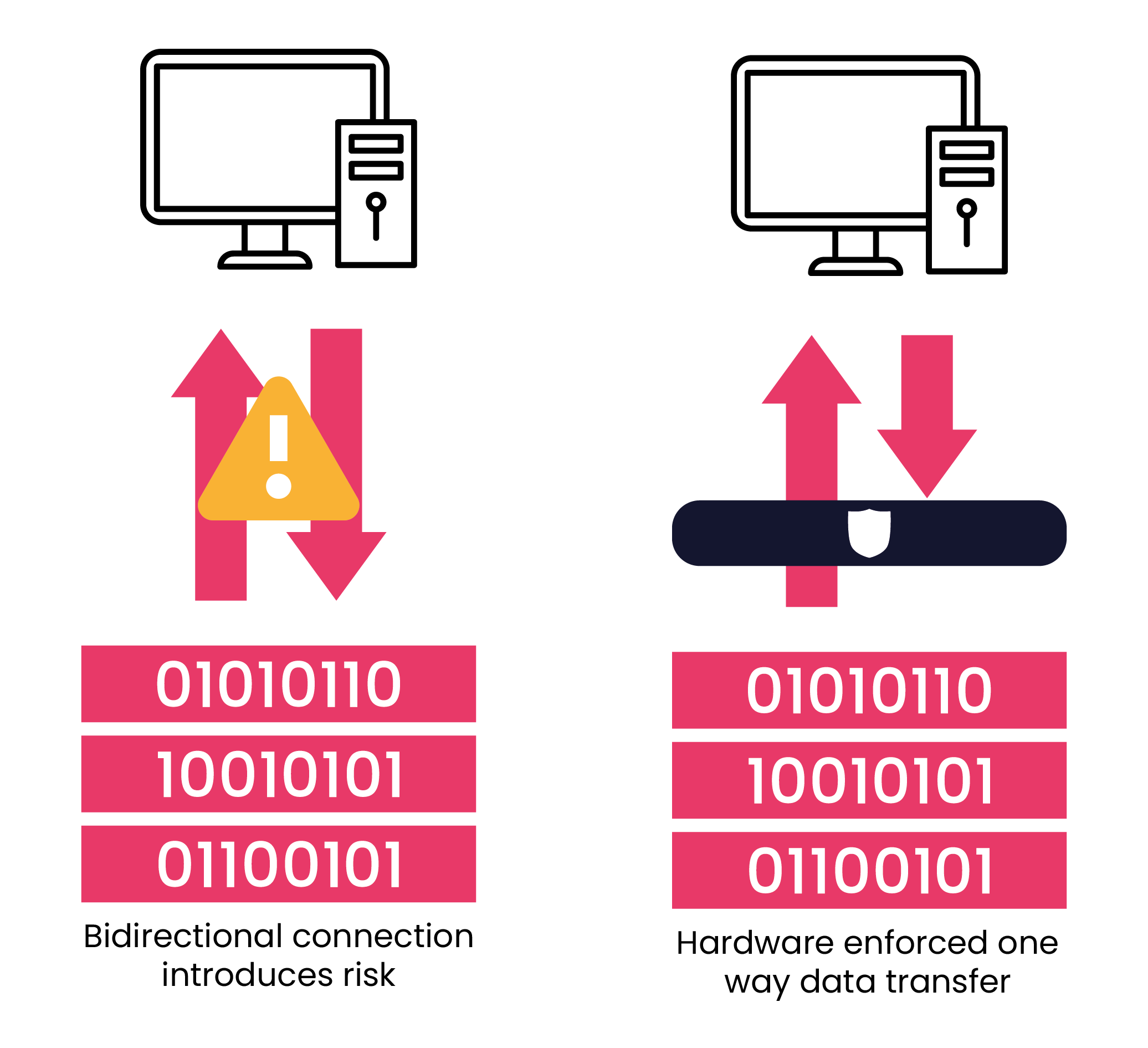
However, directly connecting IT networks or external platforms to control systems introduces risk. Industrial environments typically contain systems that were not designed with modern cybersecurity threats in mind.
Once a bidirectional network connection exists, attackers may gain pathways into critical systems.
For sectors such as energy and utilities, the consequences can be severe:
- Operational disruption
- Safety incidents
- Production outages
- Regulatory penalties
This is why many critical infrastructure operators rely on unidirectional architectures, where operational data can leave the network but nothing can return.
What IEC 63452 Defines
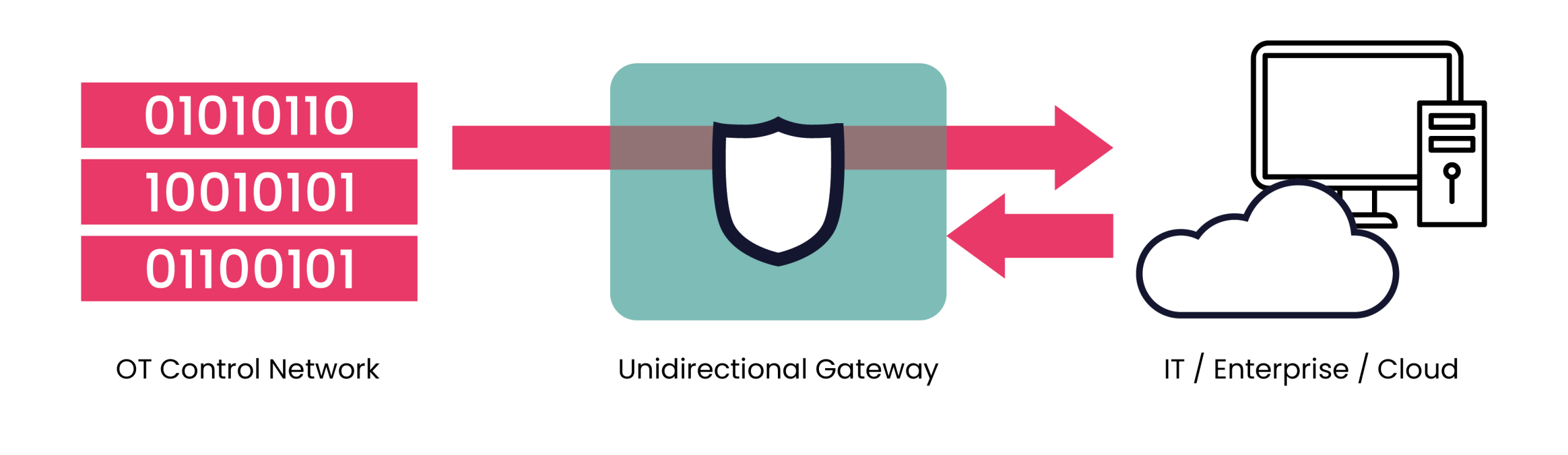
IEC 63452 provides international guidance for implementing unidirectional gateway architectures, commonly referred to as data diodes.
The standard focuses on ensuring that systems designed to transfer data out of a secure environment cannot be used to send traffic back in.
The core principles include:
Hardware-Enforced One-Way Communication
IEC 63452 describes architectures where communication is enforced physically through hardware rather than relying solely on software controls.
In these designs, a gateway allows information to flow in only one direction, making it impossible for external systems to send commands or malicious traffic into the protected network.
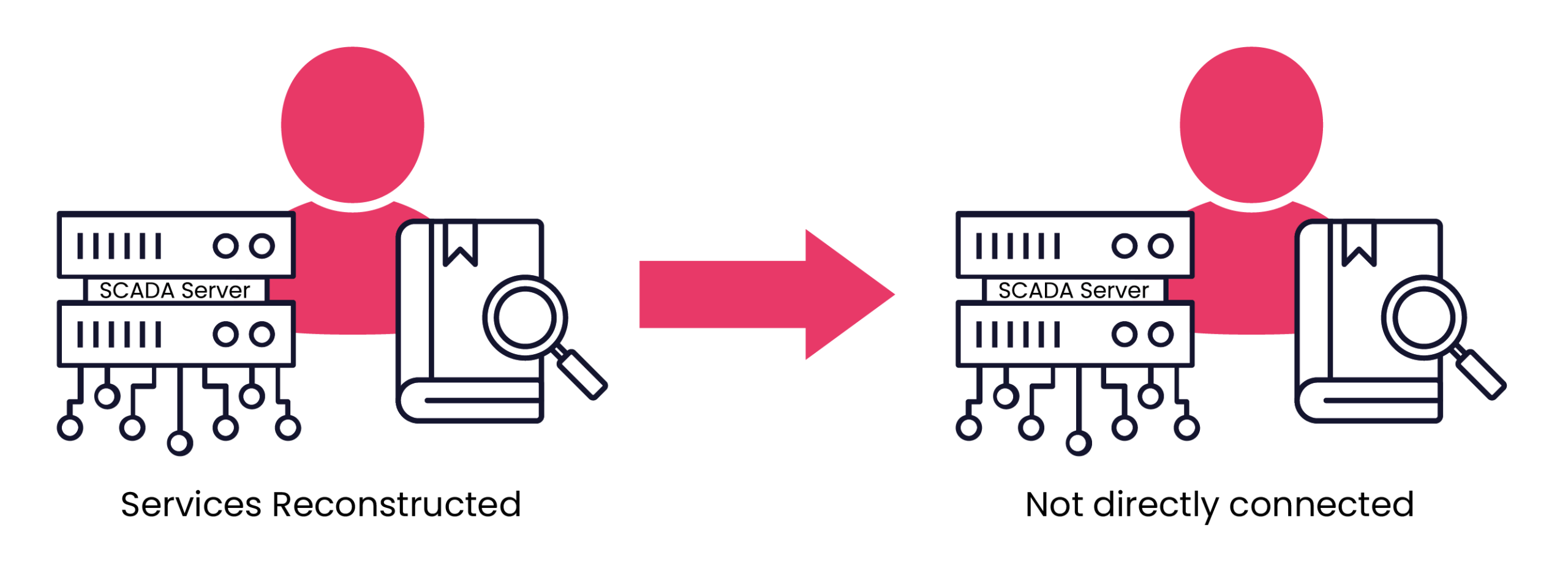
Secure Data Replication
Many industrial protocols assume bidirectional communication. To support operational use cases, the standard describes techniques for replicating or reconstructing services on the receiving side of the gateway.
These may include:
- File transfers
- Database replication
- Industrial telemetry
- Logging data
- Monitoring feeds
Rather than allowing a direct protocol session across networks, the data is rebuilt on the external side.
Architectural Guidance
IEC 63452 also provides guidance on where unidirectional gateways should be deployed within industrial environments.
Typical placements include between:
- OT networks and corporate IT networks
- Control systems and remote monitoring systems
- Industrial environments and cloud platforms
The architecture ensures that critical control networks remain isolated from external threats.
Assurance and Verification
Because unidirectional communication is fundamental to the security model, the standard also addresses verification and assurance.
This includes ensuring that:
- The gateway truly enforces one-way communication
- There are no hidden return paths
- The architecture cannot be bypassed through configuration or network behaviour

Why IEC 63452 Matters for Critical Infrastructure
While many cybersecurity frameworks address industrial systems, few standards focus specifically on secure one-way data transfer.
IEC 63452 complements broader frameworks such as:
- IEC 62443
- NIST SP 800-82
These frameworks describe segmentation and defence-in-depth, while IEC 63452 focuses specifically on the implementation of unidirectional communication technologies.
For organisations operating critical infrastructure, this approach offers several benefits:
Reduced Attack Surface
By removing the possibility of inbound communication, many remote attack vectors are eliminated entirely.
Protection of Legacy Systems
Many industrial control systems cannot be easily patched or upgraded. Unidirectional gateways provide protection without modifying the underlying systems.
Safe Data Sharing
Operators can still share operational data with enterprise platforms, security monitoring systems, and analytics tools.
Regulatory Alignment
Many regulatory frameworks increasingly expect strong segmentation between OT and IT environments. IEC 63452 provides guidance for achieving this.
Typical Industrial Use Cases
In practice, IEC 63452 architectures are commonly used in scenarios such as:
- Sending SCADA telemetry to corporate monitoring systems
- Exporting process data to cloud analytics platforms
- Feeding industrial logs into security monitoring systems
- Replicating historian data for reporting or analysis
In each case, the key principle remains the same:
Operational data can leave the control environment, but no commands or traffic can return.
Implementing IEC 63452 in Practice
Deploying a unidirectional architecture involves more than simply installing a gateway.
Organisations must consider:
- Network architecture
- Protocol handling and data replication
- Security monitoring integration
- Operational workflows
- System resilience and reliability
Getting these elements right is essential to ensure that the architecture supports operational needs while maintaining strong security controls.
Working with a partner to implement unidirectional architecture
Implementing unidirectional architectures in industrial environments requires both OT security expertise and practical deployment experience.
When finding a partner, look for operators with experience across critical infrastructure sectors that can design and deploy secure data transfer solutions aligned with IEC 63452 principles.
Their work should include:
- Designing secure OT/IT network architectures
- Deploying data diode and unidirectional gateway solutions
- Integrating protocol replication and data services
- Supporting secure monitoring and analytics pipelines
- Ensuring solutions align with industrial cybersecurity frameworks
With growing pressure on operators to share operational data while maintaining strict isolation of control systems, unidirectional architectures are becoming an increasingly important part of OT security strategies.
Final Thoughts
As industrial organisations continue to modernise their operations, the need to balance connectivity and security becomes more critical.
IEC 63452 provides a practical framework for achieving this balance by defining how unidirectional communication technologies can be used to protect critical systems while still enabling valuable data flows.
For OT professionals responsible for securing operational environments, understanding and implementing these principles is an important step toward building resilient industrial networks.
If your organisation is exploring secure ways to share OT data without increasing cyber risk, it may be time to start the conversation.
4Secure would be happy to help.
By Alex Ball, Head of Commercial
Alex Ball is a seasoned cybersecurity professional with nearly 30 years providing critical cyber solutions. He has worked across Finance, Energy and Critical National Infrastructure with additional focus on airports and rail networks. Alex works in delivering secure data exchange and cross domain solutions that unlock strategic insight and digital transformation.
