A statement on adversarial AI
The emergence of adversarial AI systems, alongside the wider proliferation of autonomous offensive tools now likely to emerge, is a real shift in the threat landscape. These systems compress the time between a vulnerability being discovered and a vulnerability being...
UK NCSC Cross Domain Guidance
On the 21st of April, the NCSC published new guidance on cross domain approach and architecture. If you work anywhere near defence, intelligence or critical infrastructure it's worth reading in full. For years, "cross domain solution" has been shorthand in procurement...
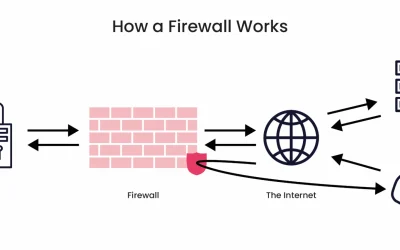
How Do Data Diodes Compare to Firewalls?
Many of today’s modern businesses are undergoing digital transformation by embracing remote work, adopting cloud computing, and incorporating Internet of Things (IoT) devices as part of their information security strategy. Such transitions need to be done securely to...
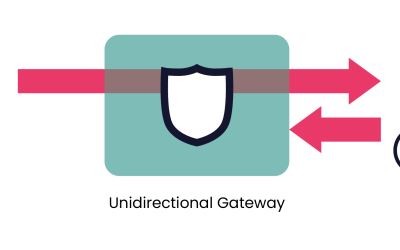
What Is a Data Diode? Learn About One of Our Core Technologies
If you've ever wondered about the science behind data diodes – such as how the technology outperforms firewalls and traditional intrusion detection/protection systems to safeguard critical networks – you're in for a real treat. In this post, we're going to explore how...
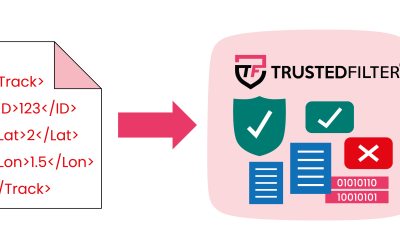
IEC 63452
Operational Technology (OT) networks are under increasing pressure to share data with enterprise systems, cloud analytics platforms, and security monitoring tools. At the same time, industrial operators must ensure that these connections do not introduce cyber risk...
Tactical Data Links
Tactical Data Links are a foundational element of modern military operations. They provide the mechanism by which platforms’ sensor tracks are exchanged and operators view time-critical information such as identification data, mission status, and command intent. By...
IT and OT Convergence: Bridging the Gap with IoT
Today’s businesses operating in industrial environments straddle two worlds: one is operational technology (OT), and the other, quickly expanding, is informational technology (IT). Up until recently, these areas were kept completely separate, sharing little...
Achieving OT to cloud convergence through cybersecurity
Did you miss our recent webinar where we explored OT to cloud convergence? Perhaps you'd like to watch the recording (available here) but you don't have time? No need to worry, I have you covered! The following is a written summary of our webinar and steps on how can...
Turning NATO’s digital backbone vision into reality, one trusted data flow at a time
When I moved from consulting and delivery into the secure data space, I didn’t expect my experience with complex, interdependent systems to be quite so relevant. But as NATO sets its sights on becoming a truly data-centric alliance, it’s clear that hands-on delivery...
Full Stream Ahead: Why Cross Domain Needs a Rethink
Since joining the 4Secure team, I’ve had the chance to dive deep into a subject that’s quickly gone from “that sounds interesting” to “why aren’t more people doing this already?”… streaming data securely between classified and sensitive domains. If you’ve worked in or...