Tactical Data Links are a foundational element of modern military operations. They provide the mechanism by which platforms’ sensor tracks are exchanged and operators view time-critical information such as identification data, mission status, and command intent. By enabling a shared situational picture, these protocols support coordination and faster decision-making.
They are widely used because they are deterministic, bandwidth-efficient, and resilient. Many are designed to operate in contested or constrained environments and therefore rely on compact, binary encodings and structural rules. While highly effective operationally, these characteristics can also make TDL messages opaque to modern security controls: without additional processing, they are essentially streams of bytes with limited semantic value on the wire.
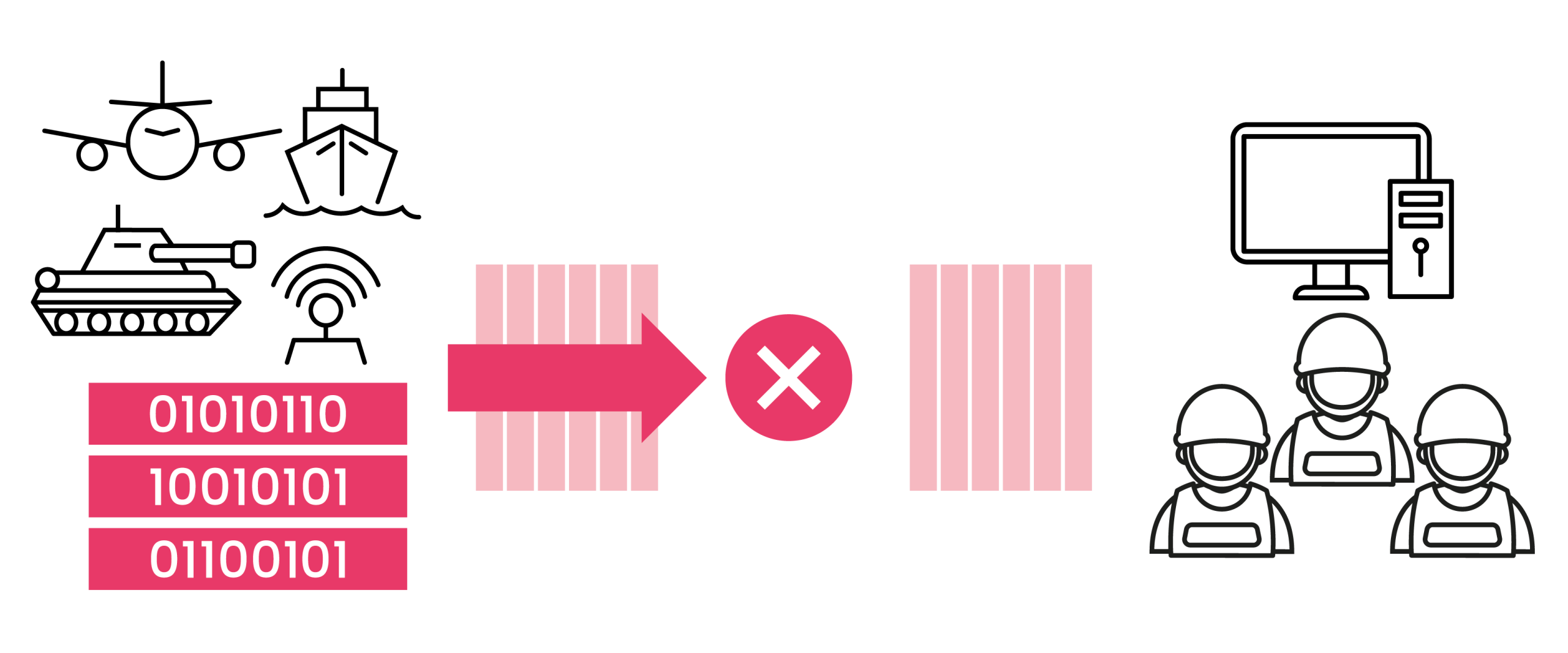
In practice, data often needs to move between systems operating at different security classifications. For example, sensor data generated in the field a less trusted network may need to be selectively transitioned to a higher classification environment to support operations, mission rehearsal, or upstream command activity. Conversely, inputs from a higher classification domain may in some circumstances need to be selectively shared into lower-assurance environments with granular control over what is shared. Any such transfer must be mediated by a Cross Domain Solution (CDS) to ensure that only authorised information crosses the boundary and that policy is enforced with high assurance.
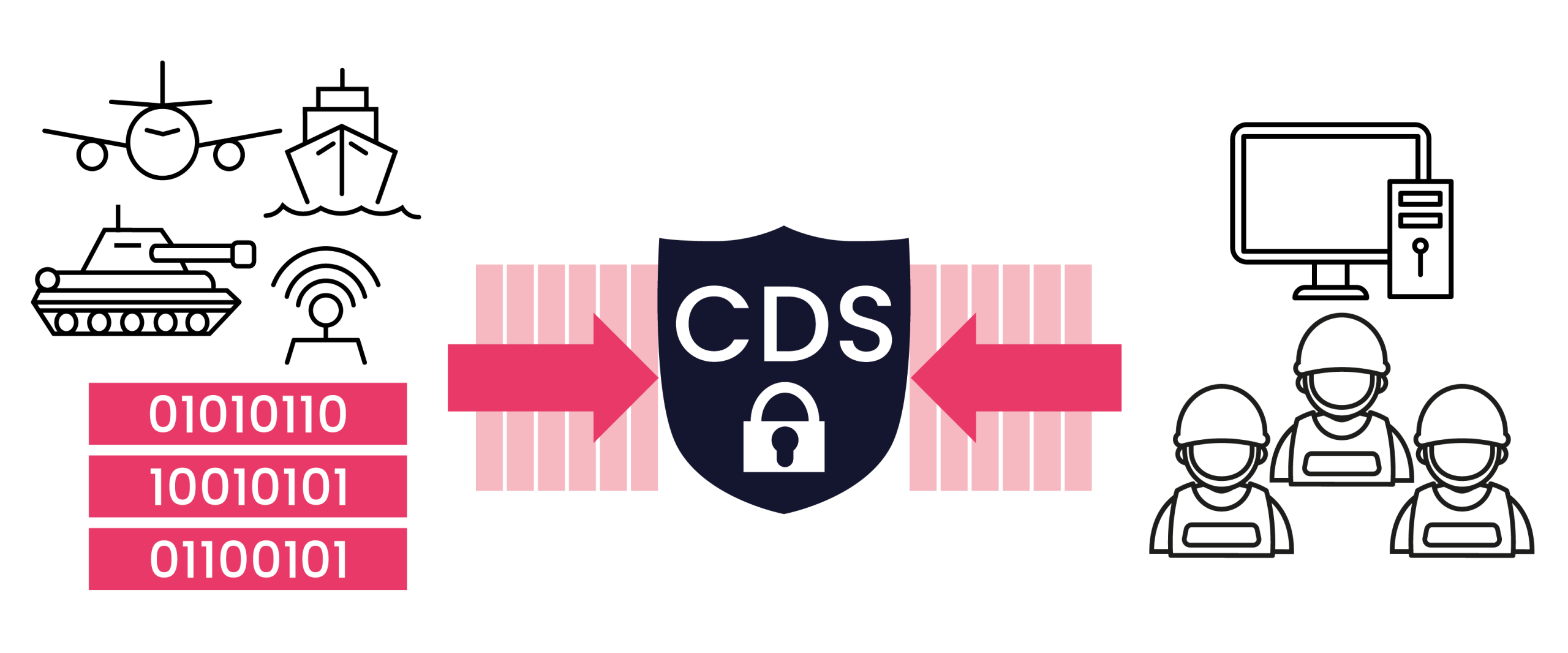
At 4Secure, one of the ways we support these complex streaming data streams by combining Apache Daffodil in our “Daffodil Accelerator” Proxies, TrustedFilter®, and Data Diodes. This architecture is designed to make tactical data both inspectable and controllable without undermining the operational characteristics that make these systems effective.
Daffodil implements Data Format Description Language (DFDL), a language allowing complex data formats to be described and parsed formally using schemas. DFDL was developed by our long-standing partner, Owl Cyber Defense. These schemas define exactly how binary datalink messages are parsed and serialised, down to the bit level. Using Daffodil, previously opaque messages can be transformed into structured representations suitable for inspection, validation, and policy enforcement.
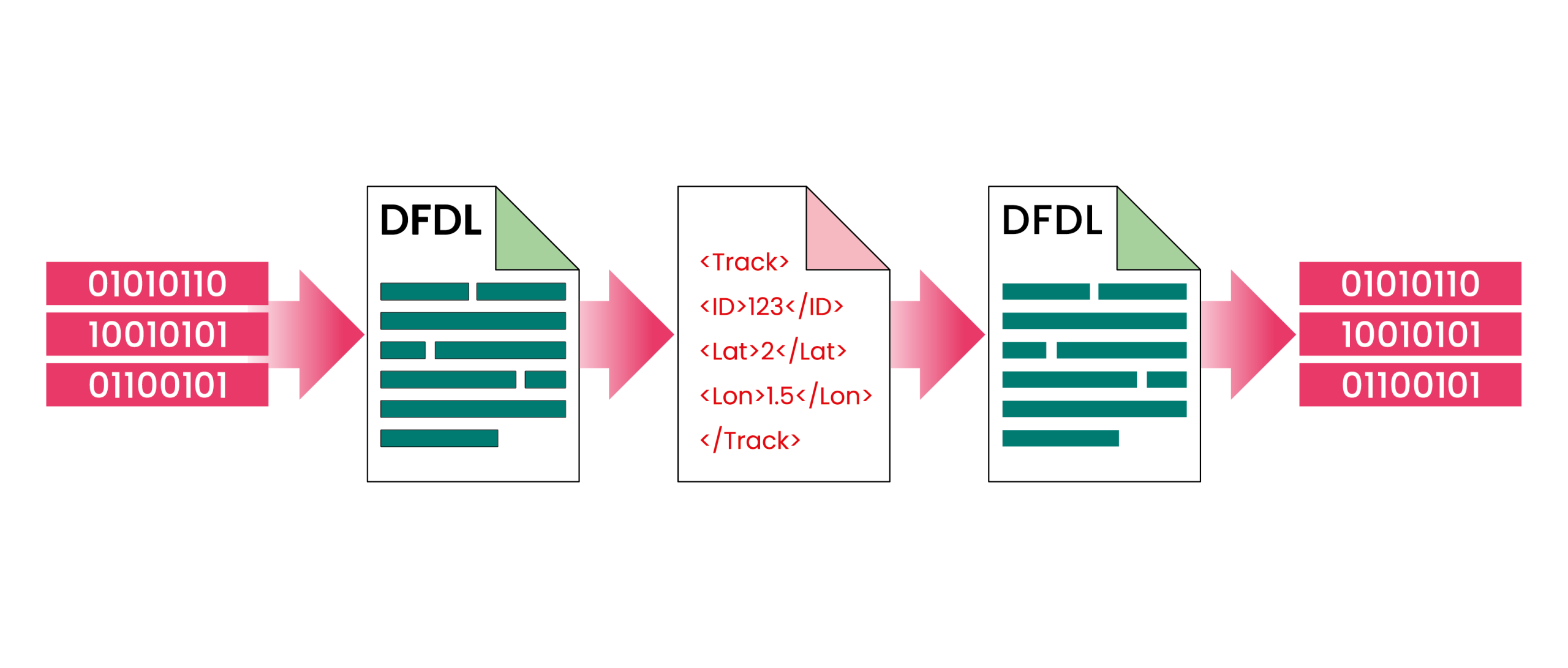
Our Daffodil Proxies are responsible for data preparation and presentation to the CDS, flexible network proxies for streaming binary messages. On ingress, they parse messages using DFDL schemas and expose their semantic content as a markup language. On egress, they re-serialise approved data back into its native binary format with full structural and semantic correctness.
Between these adapters sits TrustedFilter®, which performs policy-based semantic verification at a granular level. Rather than making decisions purely on message type or format compliance, TrustedFilter® can be leveraged to evaluate individual fields, values, and relationships against mission-specific policy. This enables precise control over what information is allowed to cross the security boundary and under what conditions.
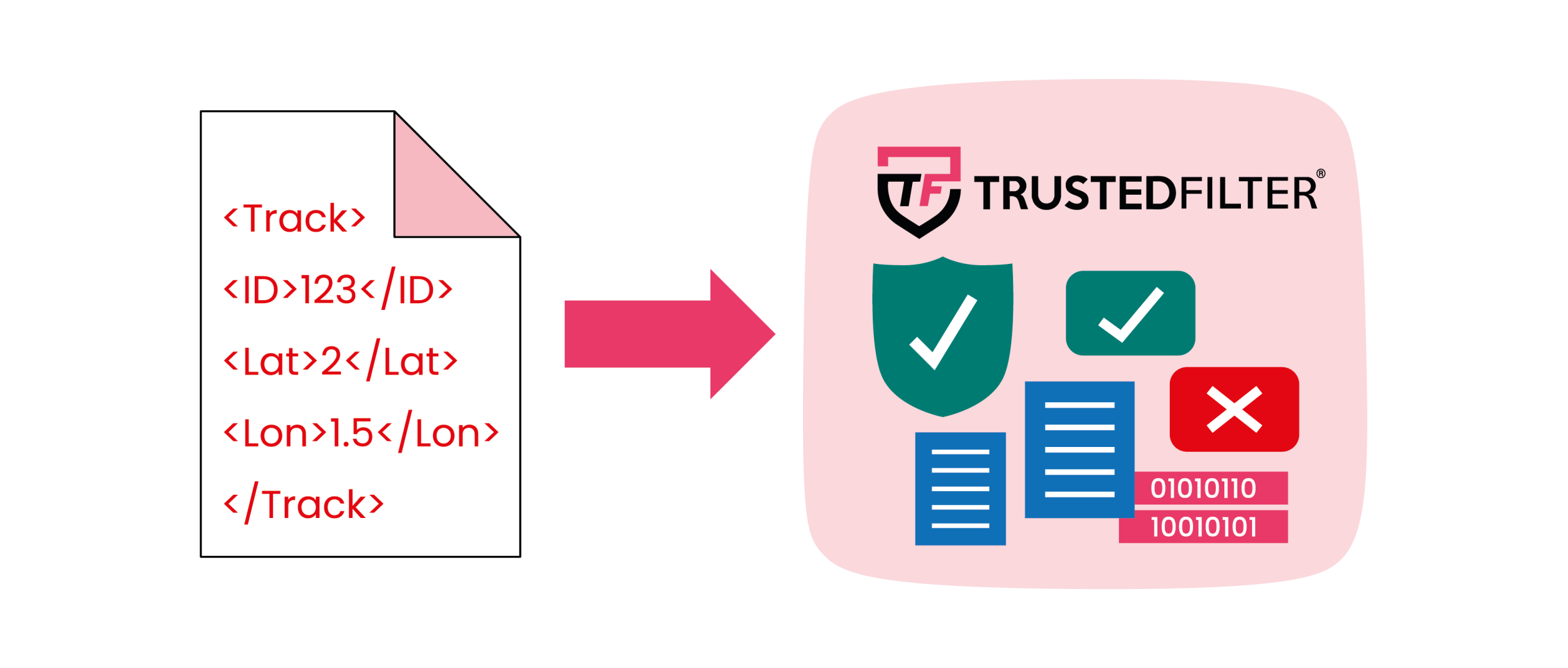
A critical benefit of this approach is customer control. While TrustedFilter® can be used to prepare data also, Daffodil is an open standard that can be independently verified, implemented and understood. Schemas can be wholly owned and maintained by the user, allowing a user to define and modify data structures to meet evolving mission requirements. Adjustments to the data structure, how it’s prepared and how it’s presented, do not require bespoke development or spiralling professional services, reducing dependency and increasing operational agility.
This pattern demonstrates how schema-driven data handling and semantic policy enforcement can be applied to tactical data links, enabling secure, auditable, and adaptable cross-classification information exchange while preserving the assurance requirements of accredited CDS deployments.
If you need help unlocking the full advantages of tactical data links, then 4Secure are always happy to help.
By Sam Black, Technical Director
Sam Black is a seasoned cybersecurity professional with a specialty in high level network defence, data-centric security and Cross Domain Solutions. He leads the Engineering and Development teams at 4Secure in delivering secure data exchange solutions that unlock strategic insight and digital transformation. Sam has extensive experience working across Government, Defence and Critical National Infrastructure.
