Hardware-Enforced One Way Data Flow
Data diodes are hardware-based devices with two separate circuits that establish one-way data flow, maintaining physical separation between networks. 4Secure design and implement robust Cross Domain Solutions that leverage the power of data diodes to enable secure, one-way data flows between critical systems. 4Secure also act as Owl Cyber Defense‘s exclusive European distribution partner.
Whether you’re connecting IT and OT environments, facilitating multi-domain operations, or looking to eliminate high-risk air gaps, we help you do it with precision, assurance, and future-proofed resilience.
Data diode data sheets
Owl OPDS-1000

The Owl OPDS-1000 is a highly integrated, all-in-one, 1U, rack-mountable data diode that
provides secure, high speed data transfers. Proven across Defence and Commercial environments.
TrustedFilter Appliance®
TrustedFilter® Appliance is an enterprise-grade, one-box Cross Domain gateway enabling secure, real-time information sharing between networks of different security levels.
4Secure VARA

VARA CDS combines 4Secure’s TrustedFilter® software with Oakdoor’s hardware-
enforced one-way data diode technology to deliver a UK sovereign, high-assurance Cross Domain Solution
What is a data diode?
A data diode is a hardware device that enforces unidirectional data flow, guaranteeing that information can move from one network to another, but never back. It’s a simple but powerful concept that underpins many of the world’s most secure networks.
Unlike traditional security tools that rely on software configurations data diodes are secure by design, removing entire classes of cyber threats from consideration.
Why 4Secure?
4Secure are solution architects, not diode manufacturers. Our expertise is building environments where data diodes are integrated seamlessly and effectively.
Our work spans multiple sectors, from defence to Critical National Infrastructure (CNI), always tailored to the operational and security realities of our clients. Our flexible, vendor agnostic approach ensures the right solution for your unique environment
Eliminating Air Gaps
Air-gapped systems have long been seen as a gold standard for isolation. But in reality, they introduce new risks. Many air gaps are breached daily via USB sticks, introducing a major vector for malware and insider threats.
Our diode-based architectures provide a safer, smarter alternative. They maintain the security benefits of isolation while enabling controlled, one-way data sharing – essential for system updates, reporting, and operational awareness.
IT / OT Integration
Operational Technology environments are increasingly connected, but they must remain protected. We use data diodes to bridge IT and OT networks in a way that aligns with security, safety, and operational uptime. Use cases include:
- Secure transfer of sensor data from OT to enterprise networks.
- Controlled export of logs and alerts for central monitoring.
- Compliance with NIS2 and other regulatory requirements.
Outcomes achieved with Data Diodes
Command and Control
Secure File Import
Secure Browse Down
Secure Video Transfer
Content Disarm and Reconstruction
OPC Data Transfer

Splunk Data Transfer

Logrhythm Data Transfer
TAK Data Transfer
Cloud Import / Export
TCP Data Transfer
The above is just a small sample of what is possible. If you require protocol handling for a specific protocol not listed above, please Contact Us and we’ll be happy to help.
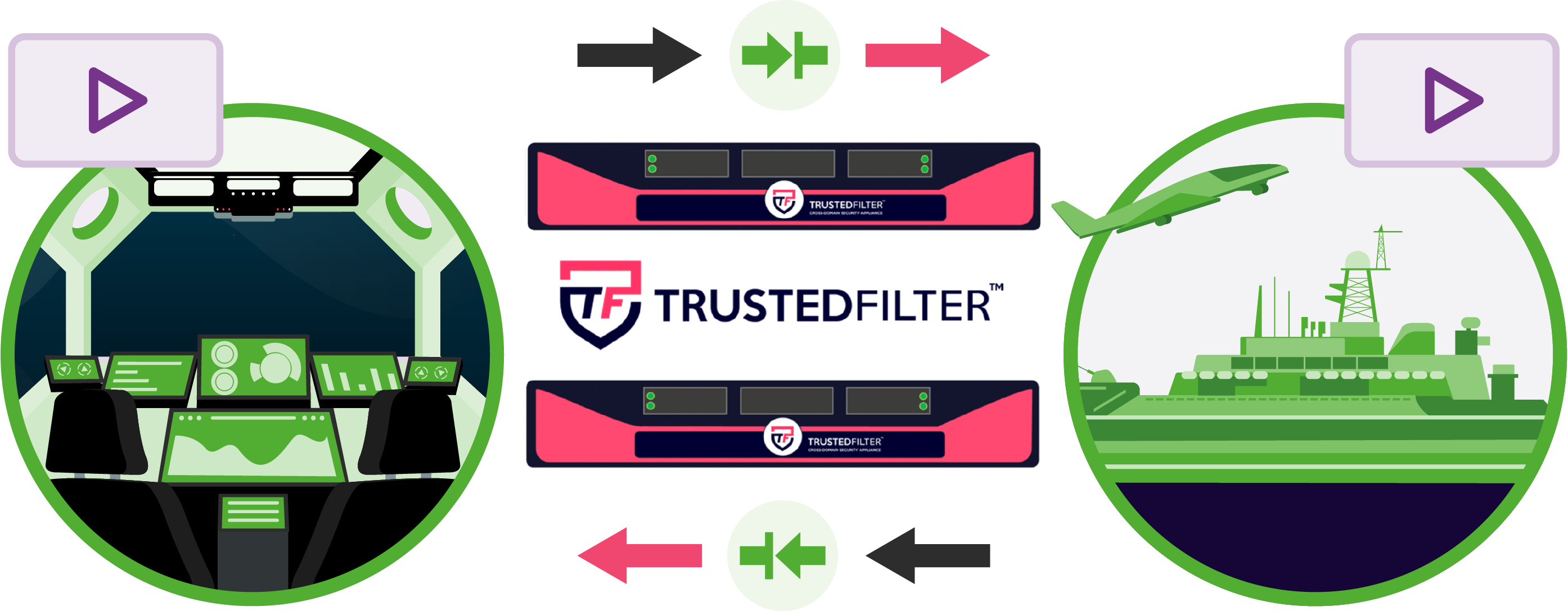
Enhance Data Diode capability with TrustedFilter® Software
While 4Secure can provide data diodes independently, our TrustedFilter® software suite enhances the capability of diodes to deliver a truly comprehensive Cross Domain Solution. TrustedFilter® adds intelligent processing to one-way data flows, enabling full content inspection and validation, data transformation across formats, and support for a wide range of protocols within secure, diode-based environments.
In many cases, TrustedFilter® can be installed directly onto the data diode itself, removing the need for additional flanking systems. This streamlines the architecture while maintaining the highest levels of assurance and control.
FAQs
What is a data diode?
Data diodes are hardware-based appliances used to enforce the unidirectional flow of network traffic. It is perhaps simplest to think of data diodes as one-way valves for data, allowing data to flow out, without a way back in.
How are data diodes different to firewalls?
A data diode is hardware enforced solution for the unidirectional flow of network traffic. Within a data diode there are two different nodes, one send only and one receive only for sending data one-way from a source to destination. This means it is against the laws of physics for data to flow in the opposite direction meaning they can’t be hacked. Firewalls on the other hand are a software-based solution, and therefore are always vulnerable to some degree of being compromised.
What is the difference between a data diode and a cross domain solution?
A data diode primarily enforces unidirectional flow control through hardware. A cross domain solution combines both hardware and software to provide feature-rich capabilities. These include handling two-way protocols in a one-way environment, performing transformation on data types into structured markup languages, as well as content inspection and data validation.
Cross-domain solutions can also be implemented for bidirectional use-cases, whereas a data-diode will only function unidirectionally.
When is additional software required on a data diode?
Many use cases necessitate software to handle inherently two-way protocols in a unidirectional environment. Most commonly this is achieved through the use of proxies, which convert two-way protocols into one-way data streams.
4Secure also overlays their proprietary TrustedFilter® software on diodes to perform content inspection and validation of data flows. Additionally, TrustedFilter® transforms complex application layer data protocols into a well-understood structured markup language for verification purposes.
What are some common use cases for data diodes?
Data diodes are typically employed for one-way data transfer between security classification domains. This can involve importing data into a more secure environment or exporting it to a less secure envrionment.
This may involve tasks such as transferring files or log data, streaming videos, or monitoring devices and endpoints.
In critical infrastructure environments, data diodes are often used to transfer monitoring data from the operational technology environment to the information technology environment.
Can a data diode be hacked?
Data diodes represent a hardware-enforced approach to unidirectional flow control. They operate on the principle that data flowing in the opposite direction is physically impossible, in adherence to the laws of physics. This stands in stark contrast to firewalls, which rely on software-based solutions and, inherently, are susceptible to exploitation.
What is a protocol break?
A protocol break involves terminating a data transfer protocol, transforming just the core data payload to an alternative protocol, and subsequently reassembling the initial protocol before the data reaches its intended destination. All 4Secure data diodes include a protocol break mechanism, which effectively hides source network details like IP or MAC addresses. This renders it infeasible for any external malicious entity to probe, dissect, or access any data related to the source network. Protocol breaks also act as a safeguard against the transmission of hidden malicious data within packet headers.
Supported Applications
Native applications supported by 4Secure Cross Domain Solutions and TrustedFilter® software. Can’t see a specific protocol? Contact us!
Modbus Transfer
Log Forwarding
Performance Management
OPC Transfer
OSIsoft PI System Transfer
Screen Replication
Remote File Transfer
DNP3 Transfer
HTTP Transfer
Advanced Messaging Queueing Protocol
MQ Telemetry Transport
Contact us
Want to know more about 4Secure’s products, services and Cross Domain Solutions? Engage with 4Secure’s specialists to find a tailored solution. The 4Secure team offer full support through 30-day proof of concept of any solution at cost to 4Secure.