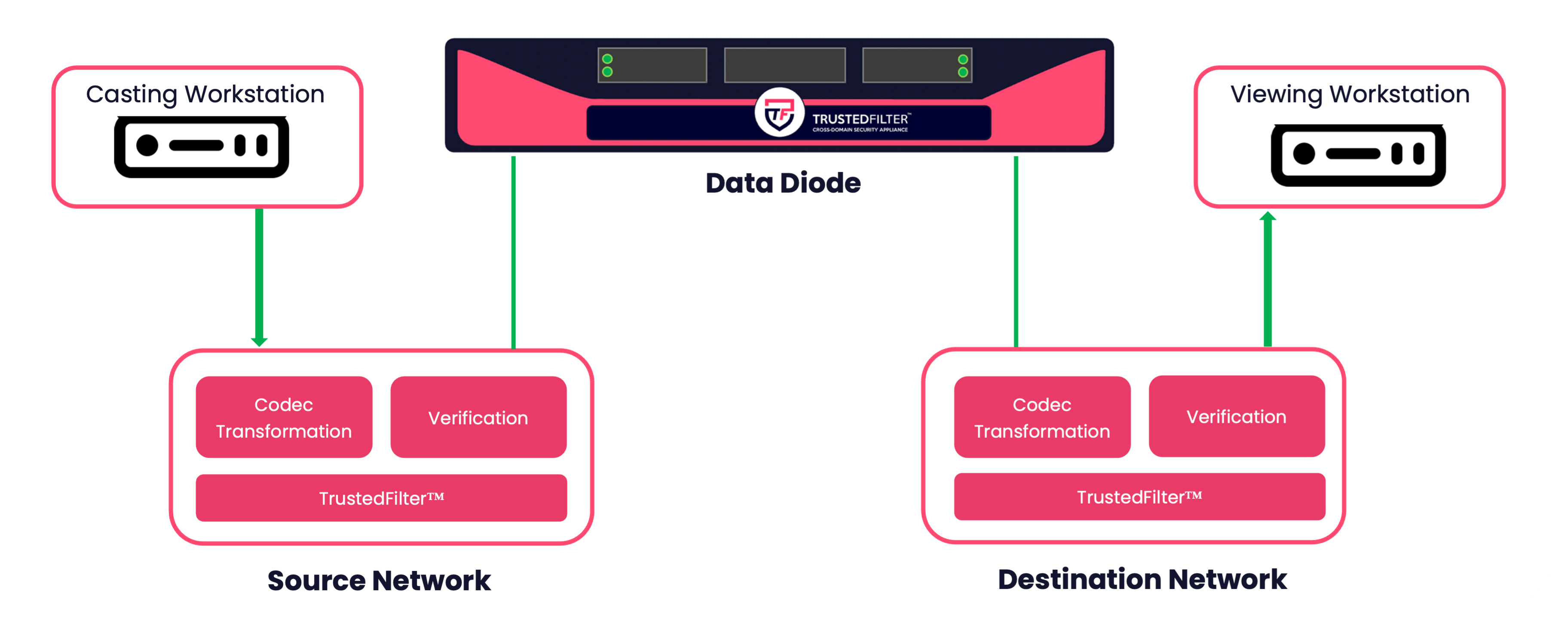
4Secure’s TrustedFilter™ platform-agnostic application transforms a video stream into a specific codec, and passes the stream across a unidirectional device into a destination network. After verifying that the stream has transformed successfully, the stream is then retransformed into its original format. If at any point an issue is detected during the transmission, the solution will stop the video stream from being transmitted to the high-security domain. Transforming a video stream into a different codec will protect against attacks on the video codec itself. 4Secure accomplish this real-time transformation and verification capability on a real-time HD video stream all within single appliance.
The 5-Step approach to Cross-Domain real-time secure video transfer with TrustedFilter™
1. Source System Caster
2. Transformation
3. Hardware Enforced Protocol Break & Air Gap
4. Verification and Retransformation
5. Destination System Viewer
The video stream is delivered to a device on the destination network where it is received by the TrustedFilter™ viewing client and made visible to users.
Enabling TrustedFilter™ Applications
TrustedFilter™ SECUREstream
- Screen casting application for securely monitoring and sharing a device screen from a low-security domain through a unidirectional appliance to a high-security domain in real-time.
- Transforms video stream codec, verifies transformation before restoring it to the original format following transmission across a unidirectional appliance.
Enabling Components
Data Diodes
A unidirectional flow control component (Data Diode) is utilised to enforce the one-way flow of data and perform a protocol break.
The all-encompassing TrustedFilter™ Appliance
For high-throughput use cases where there are multiple high-quality video streams, 4Secure adopt the TrustedFilter™ Appliance to implement this solution. The all-encompassing extensible appliance consists of a unidirectional gateway and incorporates the full TrustedFilter™ software suite to handle multiple data flows. Bi-directional model also available.
Contact Us
Want to know more about 4Secure's products, services and cross-domain solutions? Engage with 4Secure's specialists to find a tailored solution. The 4Secure team offer full support through 30-day proof of concept of any solution at cost to 4Secure.
Call for a Quick Consultation
Can't wait for a response? Call us now for a quick consultation with one of our cross domain solution specialists.