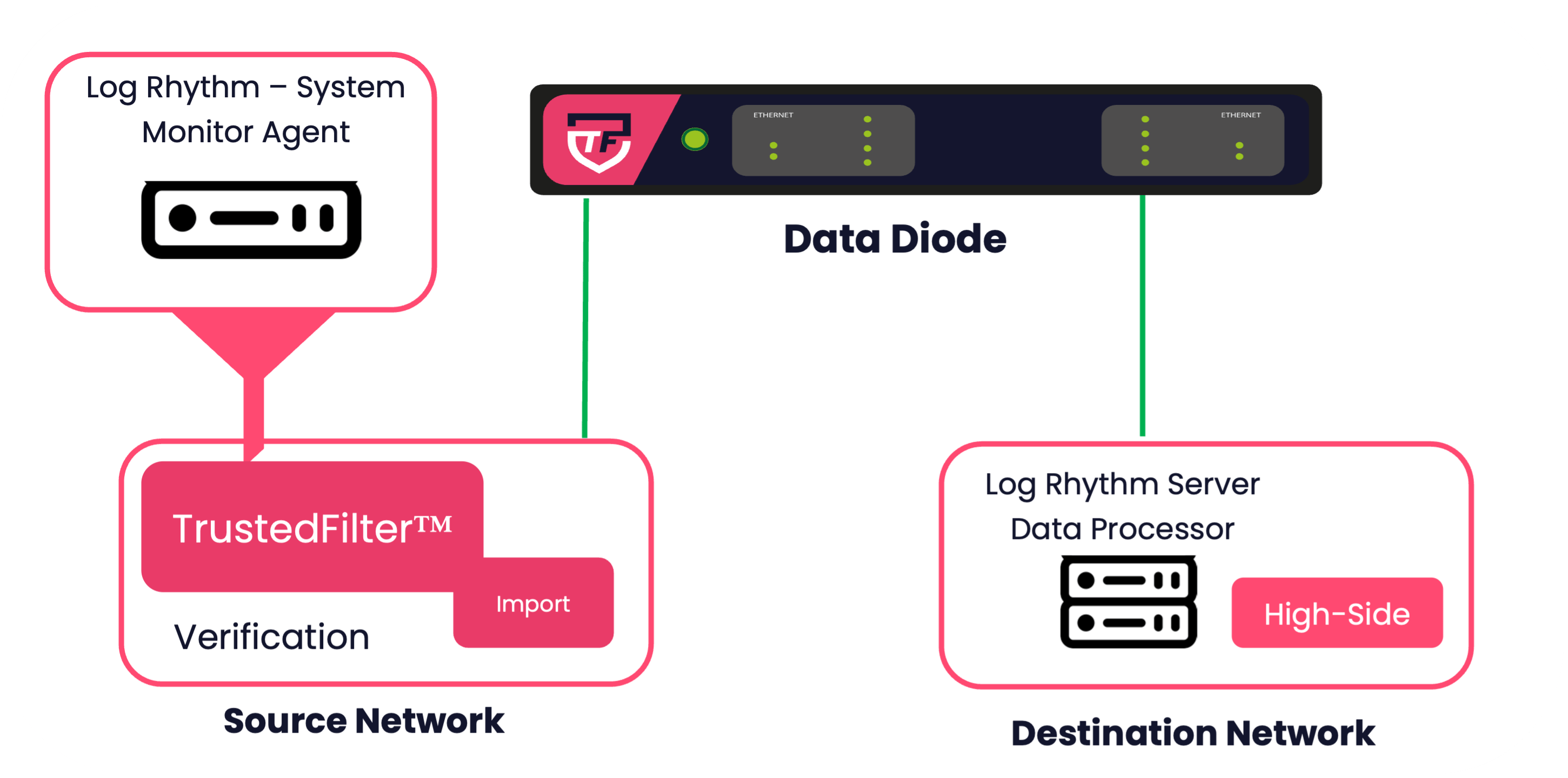
The visibility of logging information and real-time alerts originating from network devices, IoT endpoints, and applications can empower Security Operations Centre (SOC) analysts, enabling proactive actions or rapid remediation. 4Secure have delivered a solution for validating Log Rhythm agent data and ensuring it’s secure delivery through a unidirectional gateway, into the SOC on the destination network.
How 4Secure deliver a robust verification engine
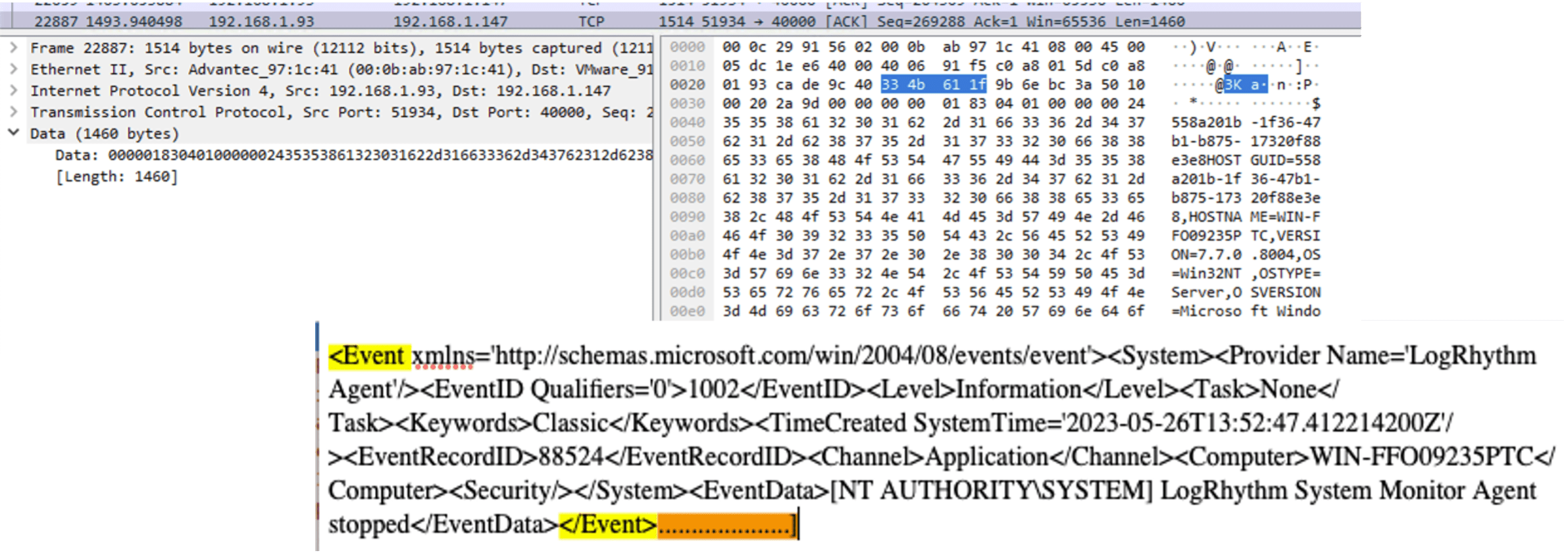
1. Packet Inspection and analysis
After performing a packet capture from a log rhythm agent installed on a windows endpoint in a controlled envrionment, 4Secure determined that the log payloads were transmitted in the form of XML enclosed within an unencrypted TCP stream. Each windows log message message was also observed to have a uniform delimiter. This consistency in structure across LogRhythm agent messages provided a foundation for building a verification engine.
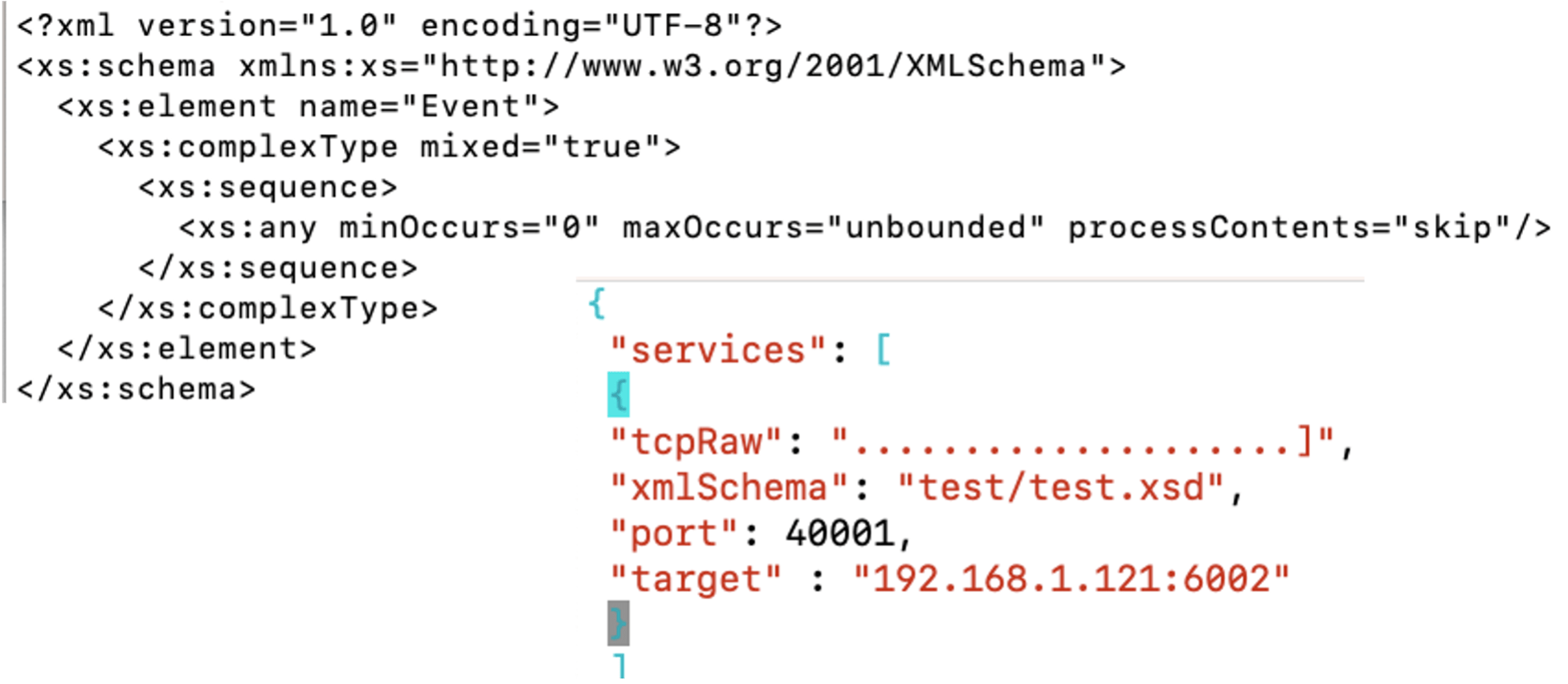
2. Verification Engine Build
Using the gathered XML data, 4Secure built an XSD schema tailored to ensure that the XML payload’s structure aligned with the anticipated format of the LogRhythm data agent. This XSD schema was customised to enforce the presence of anticipated fields and their corresponding values, while accommodating variations in XML elements that are subject to change based on the specific log message. Additionally, the identified delimiters were integrated into the verification engine, enabling the engine to accurately identify the message’s endpoint and consequently validate its content.
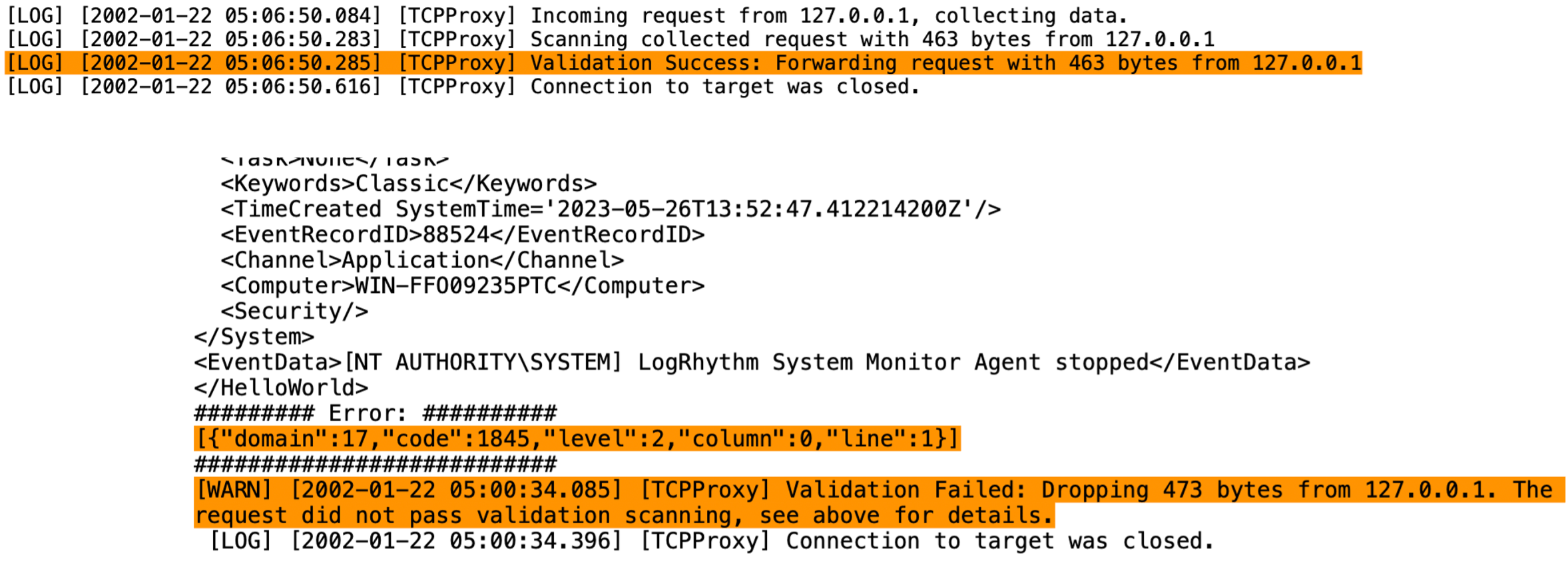
3. Testing – valid and invalid messages
Following the design of the solution, 4Secure conducted testing and observed payloads that aligned with or deviated from the criteria of the syntactic and semantic verification engine. Messages adhering to the schema successfully underwent validation and were permitted for transmission across the network boundary. Messages not conforming to the schema were rejected and the dropped message logged. The granularity 4Secure built into the verification ensured adherence to Information assurance and compliance to the NCSE import pattern.
Enabling TrustedFilter™ Applications
TrustedFilter™ SECUREimpex
- Verification engine Installed directly onto a TrustedFilter™ unidirectional gateway
- Performing syntactic & semantic verification
- XML / JSON Schema Validation
Enabling Components
Data Diodes
A unidirectional flow control component (Data Diode) is utilised to enforce the one-way flow of data and perform a protocol break.
The all-encompassing TrustedFilter™ Appliance
4Secure adopted their TrustedFilter™ Appliance to implement this solution. The all-encompassing extensible appliance consists of a unidirectional gateway, the full TrustedFilter™ software suite and boasts considerable computational power to effectively host the Cogent DataHub software. Bi-directional model is also available.
Contact Us
Want to know more about 4Secure's products, services and cross-domain solutions? Engage with 4Secure's specialists to find a tailored solution. The 4Secure team offer full support through 30-day proof of concept of any solution at cost to 4Secure.
Call for a Quick Consultation
Can't wait for a response? Call us now for a quick consultation with one of our cross domain solution specialists.