4Secure Technical Delivery Manager, Sam Black explores how organisations can go beyond NCSC guidance for importing data and enhance their data security by using TrustedFilter software as part of a cross-domain solution.
Government organisations, education bodies, pharmaceutical companies, and critical infrastructure, both public and private sector, are required to adhere to the NCSC guidance for safely importing data.
All organisations typically have segregated areas in their network environments, physically separated and disconnected to protect them from network and application-based attacks. As more organisations adopt automated solutions to move their data between security domains, the requirement for organisations to adhere to NCSC guidance for safely importing and exporting data is increasing exponentially.
The NCSC guidance offers valuable insights into secure data import techniques. However, certain use-cases require capabilities beyond the scope of the defined use cases in the import patterns. In these scenarios, many are not fully utilising the range of software options available to enhance their data security.
4Secure take a different approach to cross-domain solutions by providing full-service consultancy across hardware, software, and implementation. In essence, the NCSC guidance principles primarily target structured data within complete files. 4Secure applies these core principles to manage unstructured data and streaming protocols, facilitated through the adoption of 4Secure’s TrustedFilter software suite. TrustedFilter serves as an abstraction layer, positioned above critical elements of the cross-domain solution, including the protocol break and unidirectional flow control provided by the hardware components.
4Secure works with cross-domain architects and in-house information assurance consultants to craft solutions that are secure by design.
What are the NCSC Guidelines?
The nscs guidelines detail at length various human approaches that should be considered in the wider environments such as supply chain security, access controls, and having processes in place for what actions to take in the event malicious data is found to be imported.

Doing Things Differently
While the NCSC guidance primarily focuses on file imports and provides extensive documentation with a recommended import pattern, TrustedFilter elevates the identified defensive techniques by extending its protective features to diverse raw application and data streams sourced from any endpoint, server, or application.
4Secure’s TrustedFilter software emphasises a broader application of defence techniques to data streams that enables novel and granular control over the application and a wide and full featured support for your entire cross-domain ecosystem.

4Secure's Cross Domain Solutions
This approach instils confidence in our clients, assuring them that data imports from their applications and endpoints—beyond complete files—are conducted securely. The versatility enabled by our software empowers us to deliver enhanced capabilities and tangible benefits in real-world scenarios.
Designing from a Secure By Design Methodology
For 4Secure, the pivotal element in aligning with NCSC guidance while delivering the desired capability lies in the TrustedFilter software. Although hardware remains integral in most solutions for flow control and enforcing a protocol break, the true enabler for layering defensive techniques and implementing meticulous data verification is the TrustedFilter software.
4Secure’s rapidly expanding development team are dedicated to advancing our comprehensive off-the-shelf transformation and verification capabilities, meeting the stringent assurance requirements of the most secure and critical environments.
In advocating a collaborative approach between cross-domain architects and in-house Information Assurance consultants, 4Secure develops its cross-domain solutions using a secure-by-design methodology, crafting solutions that prioritize security from the ground up – balancing desired capability, with adherence to information assurance standards.
Implementing secure-by-design principles in the development of cross-domain solutions entails a meticulous examination of the low-level contents and structure of expected data. Once this has been achieved and data has been normalised, validation against user defined values within the data can take place, enabling the granular verification of not only the structure of the data, but also the content within to ensure it is correct in the context of the system.
NCSC Import Pattern
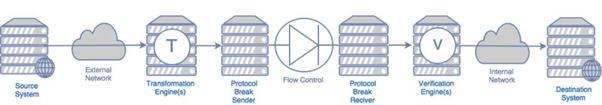
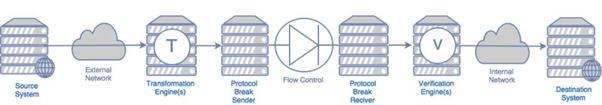
The NCSC import pattern is a recommended sequential import pattern detailing hardware and software requirements for safely importing data.
No one-size-fits-all approach
The outcome often incorporates many defence techniques outlined in the NCSC guidance, applied in conjunction with secure-by-design principles to a broader scope of applications and protocols that may not be typically implemented as part of a cross-domain solution. This approach not only delivers the desired capabilities but also fulfils assurance requirements, allowing the Senior Responsible Officer (SRO) to confidently deem the solution secure and authorised for use.
At 4Secure, we firmly reject the “one-size-fits-all” approach to cross-domain Security, embracing a tailored and innovative strategy to meet the unique demands of our clients
What are the NCSC Guidelines?
The nscs guidelines detail at length various human approaches that should be considered in the wider environments such as supply chain security, access controls, and having processes in place for what actions to take in the event malicious data is found to be imported.

NCSC Import Pattern
The NCSC import pattern is a recommended sequential import pattern detailing hardware and software requirements for safely importing data.
Beyond NSCS with Trusted Filter
Go beyond the requirements of the NCSC guidlines with TrustedFilter-based cross-domain solutions from 4Secure.
30-day proof of concept, at cost to us…
Want to know more about 4Secure’s products, services and cross-domain solutions? Engage with 4Secure’s specialists to find a tailored solution. The 4Secure team offer full support through 30-day proof of concept of any solution at cost to 4Secure.





